Measure Your Program Outcomes
Source: Based MetricStream customer responses and GRC Journey Business Value Calculator
-
 66 %
66 %reduction in the time taken to complete risk assessments
-
 37 %
37 %cost savings in risk assessment and related processes
-
 50 %
50 %time savings in tracking and linking policies to regulations
Automate and Enhance Cyber Governance, Risk, and Compliance (GRC) Processes
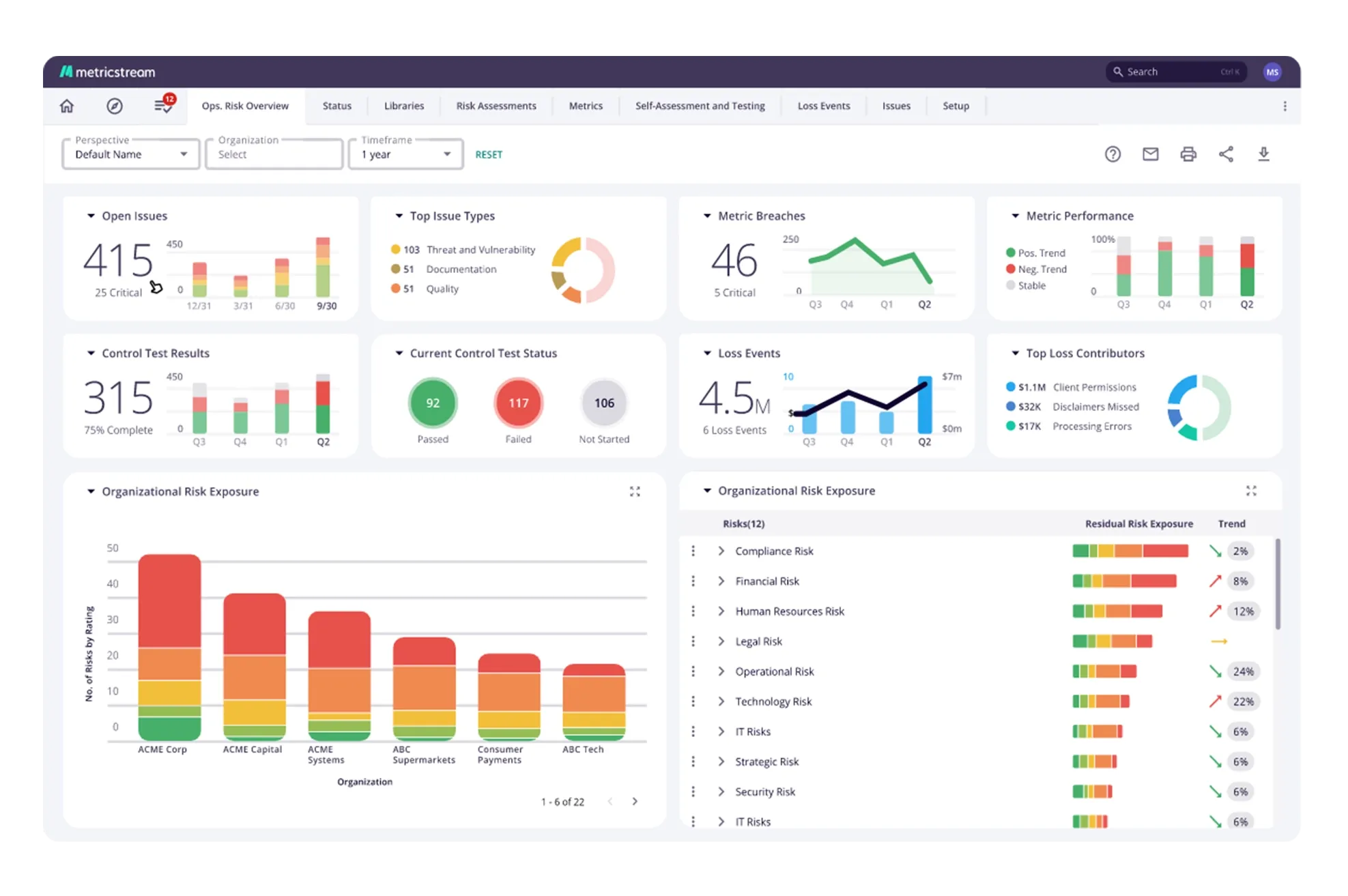
MetricStream Cyber GRC helps organizations actively manage cyber risk through an IT and Cyber Risk and Compliance Framework that aligns with established security standards so you can pass IT audits more efficiently and get buy-in from top management. Gain comprehensive visibility into the overall IT risk posture and cybersecurity investment priorities. Get your IT and Cyber Compliance program up and running quickly with pre-packaged content and industry frameworks such as ISO 27001, NIST CSF, and NIST SP800-53, and map policies to IT controls and policy exceptions. Leverage best practices, insightful reporting, and risk quantification.


How Our Cyber GRC Helps You
Adopt a streamlined, proactive, and business-driven approach to IT and cyber risk management and mitigation. Define and maintain data on IT and cyber risks, assets, processes, and controls. Assess, quantify, monitor, and manage IT and cyber risks using industry-standard IT risk assessment frameworks, such as NIST, ISO, and more. Manage issues through a closed-loop process of issue investigation, action planning, and remediation.
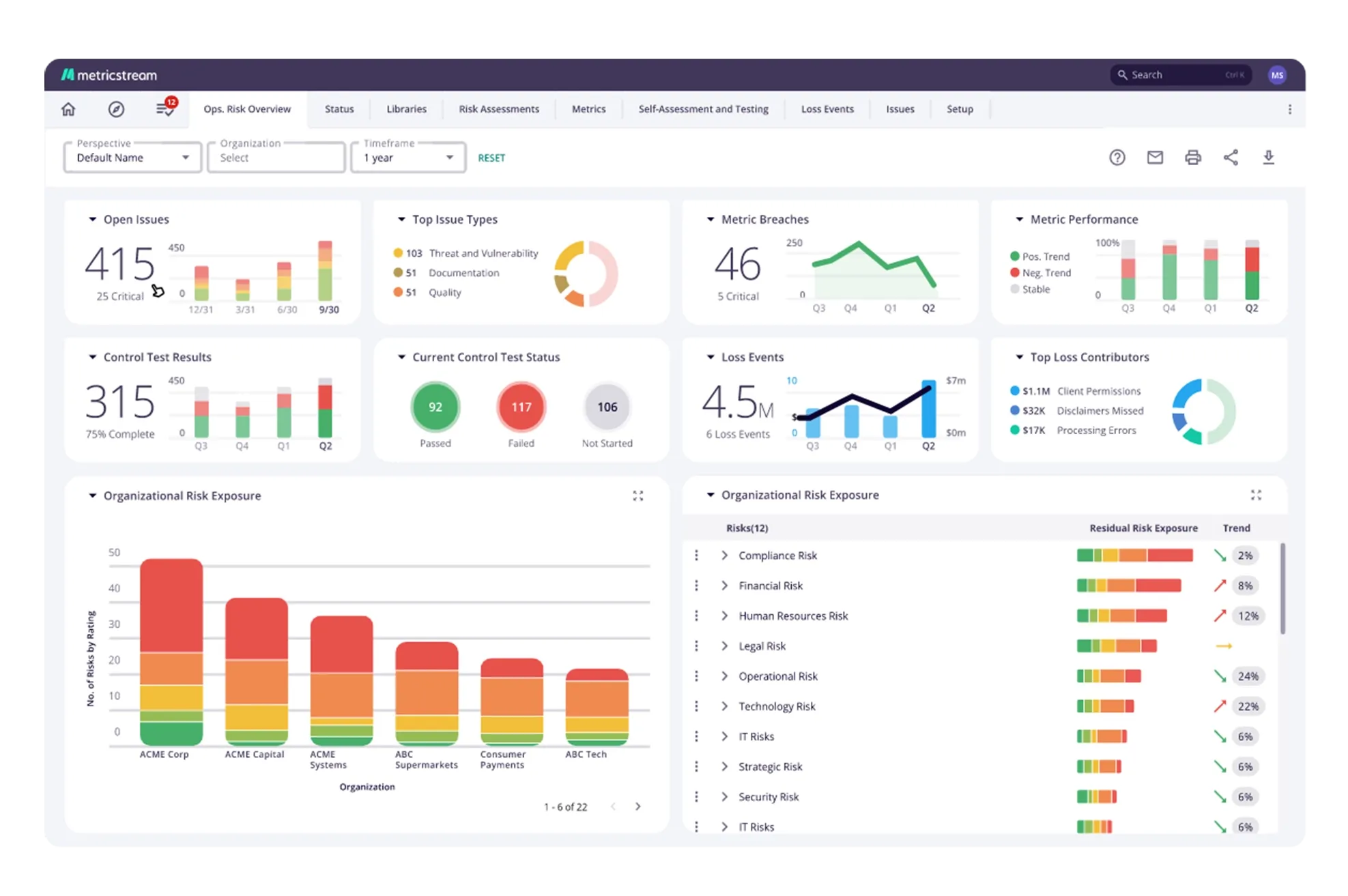
Manage and monitor IT and cyber compliance processes based on various security frameworks and standards. Create and maintain a central structure of the overall IT and cyber compliance hierarchy. Link IT and cyber compliance controls and assessment activities based on your organization’s specific security requirements. Structure and streamline the processes for documenting, investigating, and resolving IT compliance and control issues.
Enable a systematic approach to IT policy management across business units, divisions, and global locations. Easily create policies – either by entering the required information into the system or by uploading an existing policy as an attachment. Strengthen IT compliance by linking IT and cyber policies to asset classes, requirements, risks, controls, processes, and organizations. Trigger policy review and revision cycles through automated notifications and task assignments.
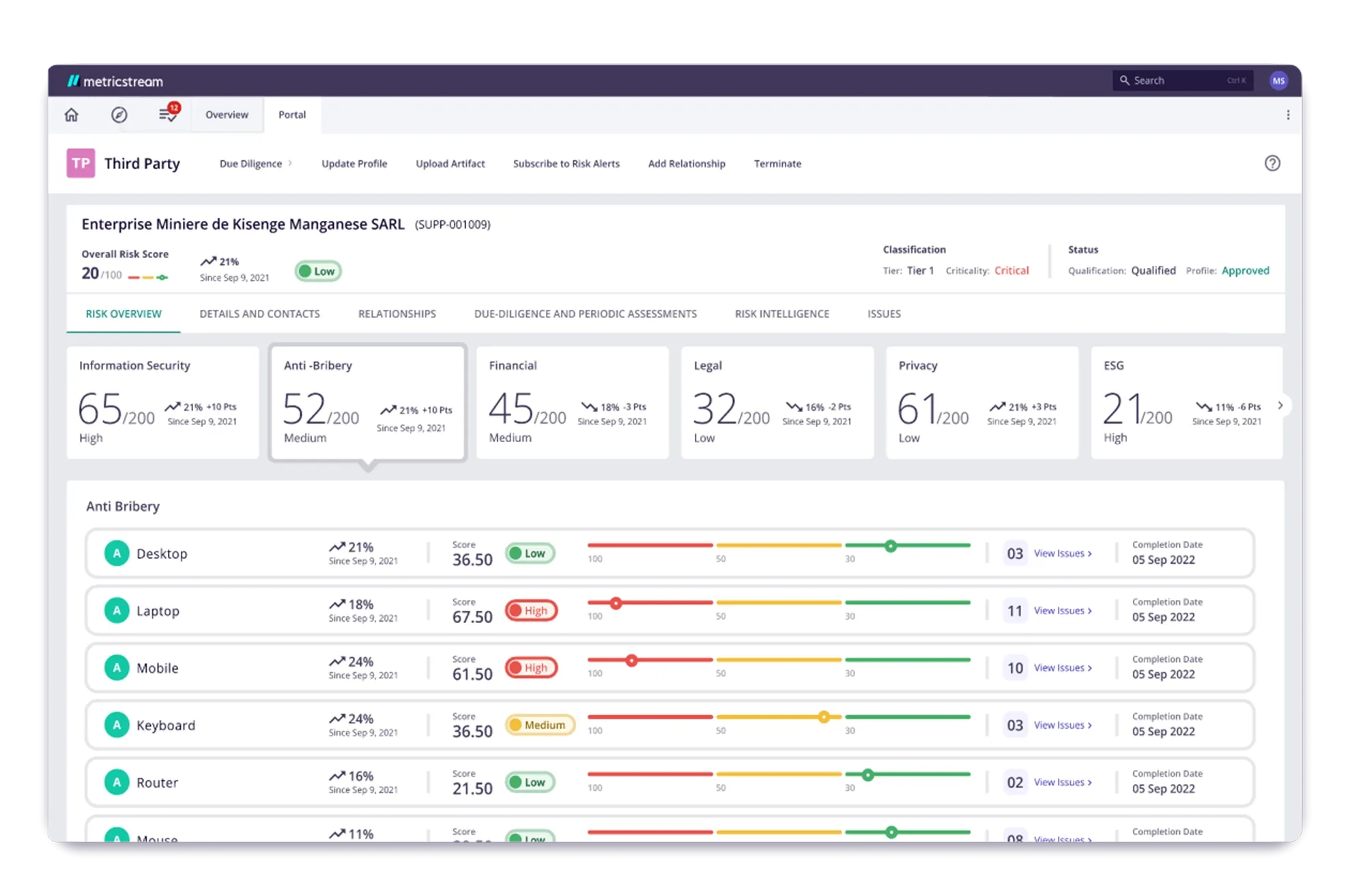
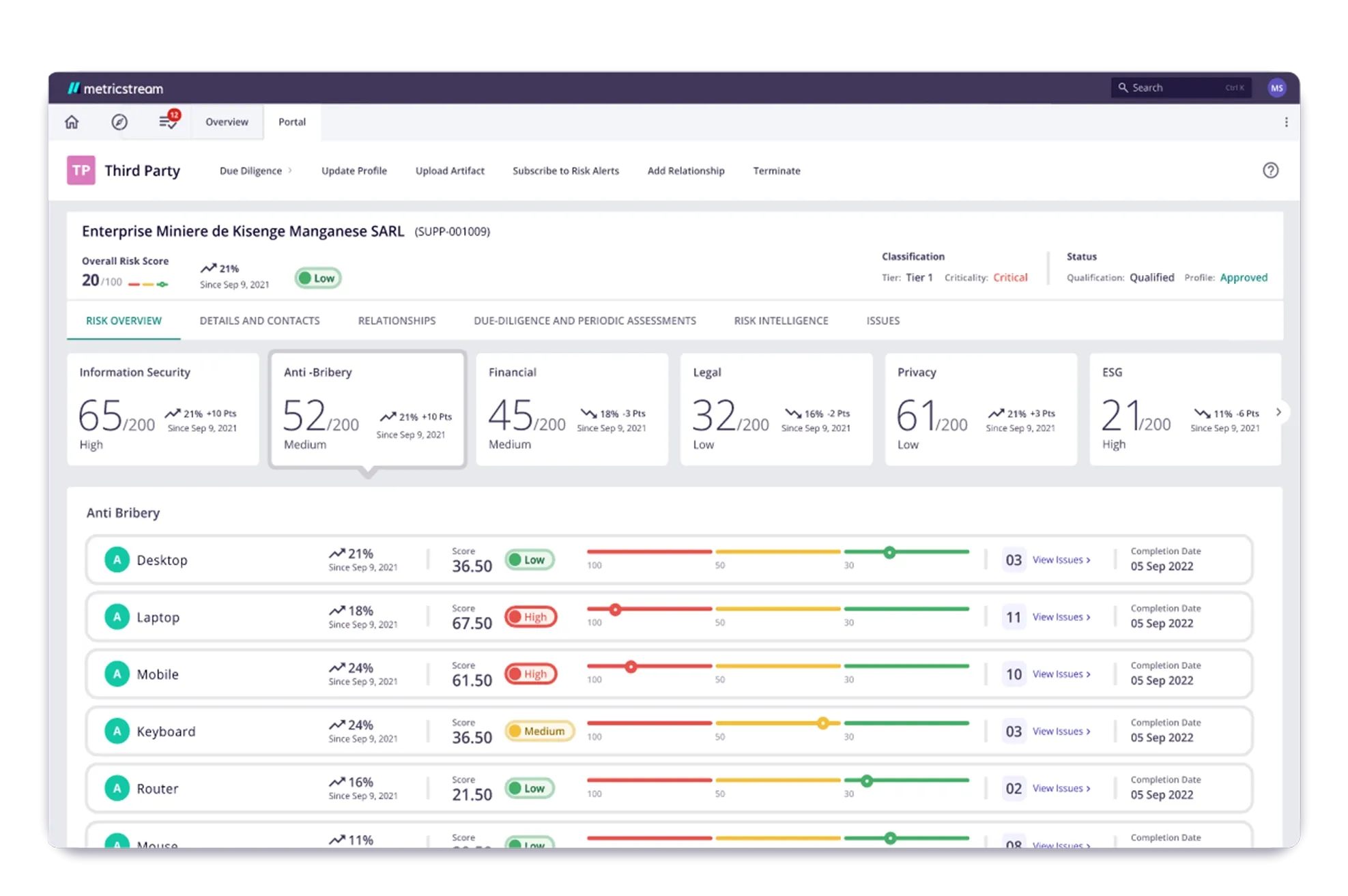
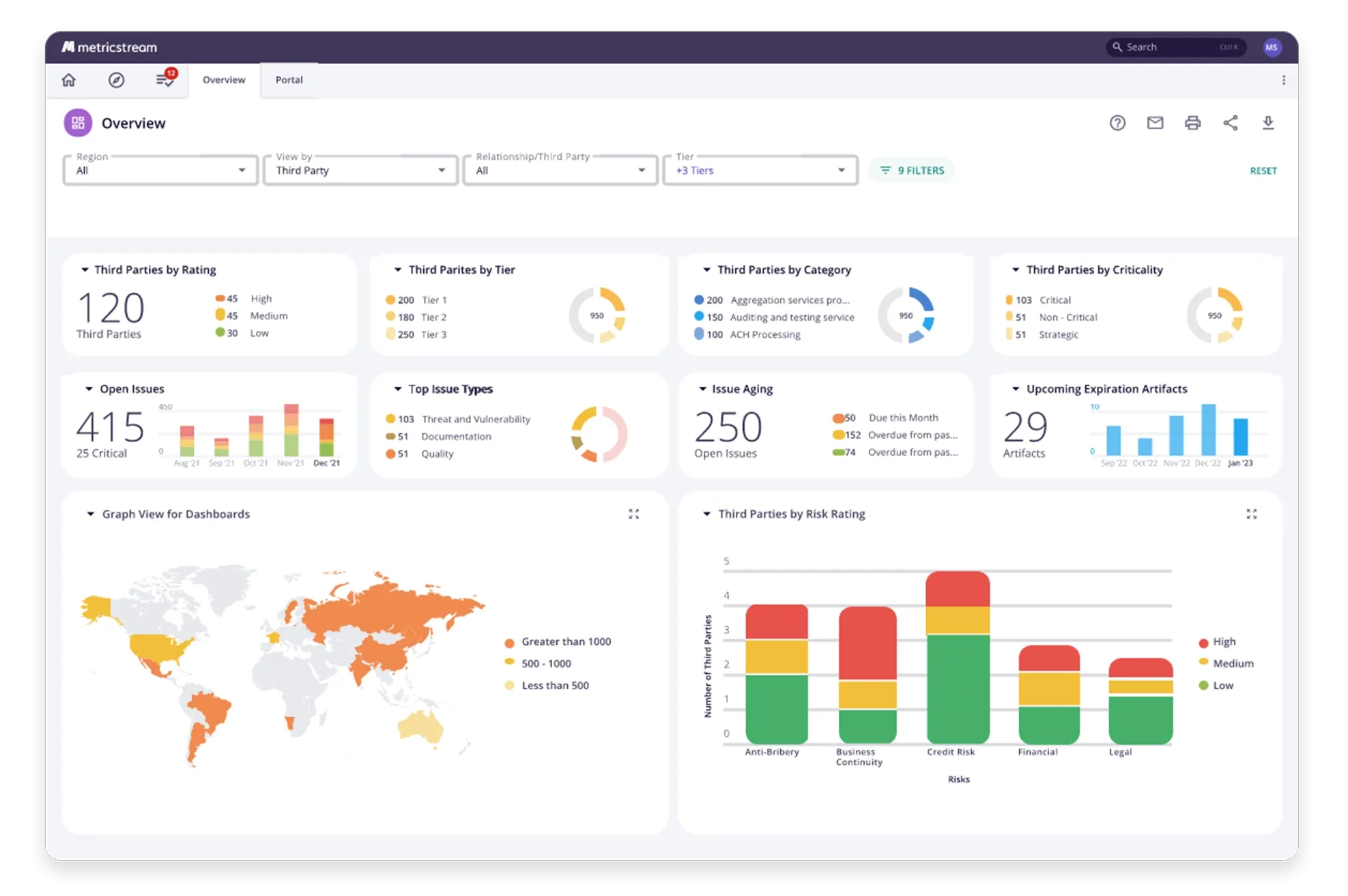
Identify, assess, mitigate, and monitor IT vendor risks while also managing vendor compliance. Leverage automated workflows to accelerate registration and onboarding processes of IT vendors, conduct risk assessments, continuous vendor monitoring, and risk mitigation. Simplify due diligence by leveraging pre-defined questionnaires to assess vendor risks. Leverage powerful reports and analytics to gain deeper insights into vendor risks, compliance, and performance.
Express your cyber risk exposure in monetary terms to analyze and communicate risk. With support from the FAIR model, accurately determine the monetary impact of cyber risks like data breaches, identity theft, infrastructure downtime, etc. Leverage simulation techniques for transforming range-based estimates into more accurate values. Enable executives to better prioritize cyber investments and drive alignment between cyber programs and the overarching risk management strategy.
How Our Cyber GRC Benefits Your Business
- Build confidence with leadership and regulators through robust enterprise-wide cyber risk management. Gain real-time visibility into threats and vendor risks, improve efficiency by prioritizing remediation, and quantify cyber risks in business terms for proactive communication and mitigation.

Frequently Asked Questions
MetricStream Cyber GRC is an AI-first product that enables organizations to rapidly implement an integrated IT and cyber risk and compliance program aligned with business and security objectives. It combines IT and cyber risk management, threat and vulnerability management, cybersecurity compliance, policy management, and vendor risk management on a single platform. The product supports industry standards including NIST, ISO 27001, and SOC 2, and provides a quantified view of cyber risk exposure to support informed investment decisions.
According to customer responses and the GRC Journey Business Value Calculator, MetricStream Cyber GRC has delivered a 66% reduction in the time taken to complete risk assessments, 37% cost savings in risk assessments and associated processes, 50% time savings in tracking and linking policies to regulations, and a 40% reduction of evidence requests through de-duplication.
MetricStream Cyber GRC expresses cyber risk exposure in monetary terms using advanced Cyber Risk Quantification capabilities. The product supports the FAIR (Factor Analysis of Information Risk) model and simulation techniques that convert range-based risk estimates into precise dollar values. Organizations can quantify the monetary impact of risks such as data breaches, identity theft, and infrastructure downtime, enabling executives to prioritize cyber investments based on business-aligned risk data rather than technical severity scores alone.
MetricStream Cyber GRC proactively identifies, consolidates, and prioritizes cybersecurity threats and vulnerabilities from multiple sources into a unified view. It determines combined risk ratings for business assets based on vulnerability severity and the asset's criticality, enabling security teams to make better-informed decisions about which vulnerabilities to remediate first. Integrations with third-party vulnerability scanning tools allow automated import of vulnerability data directly into the platform.
MetricStream Cyber GRC enables organizations to manage compliance with cybersecurity standards and frameworks, including NIST CSF, ISO 27001, NIST SP 800-53, and SOC 2, through a central compliance hierarchy that links controls, risks, policies, and assessments. Pre-packaged content covering 800+ controls enables fast implementation. Automated notifications alert stakeholders when standards change, and compliance status is tracked in real time through role-based dashboards.
MetricStream Cyber GRC includes vendor risk management capabilities that allow organizations to identify, assess, and monitor IT vendor risks throughout the vendor lifecycle. Automated workflows accelerate vendor registration and onboarding. Pre-defined questionnaires simplify due diligence, and continuous monitoring using intelligence feeds from trusted content providers keeps vendor risk profiles current. Reports and analytics provide a holistic view of vendor risk, compliance, and performance.
MetricStream Cyber GRC is designed for CISOs, IT risk managers, cybersecurity compliance professionals, and security operations teams at organizations that need to integrate cyber risk management with their broader GRC program. It is especially valuable for organizations operating in regulated industries—such as financial services, healthcare, and energy—where cybersecurity compliance must be demonstrated to regulators, and where a quantified view of cyber risk is required for board and executive reporting.
MetricStream Cyber GRC reduces evidence request duplication by linking controls across multiple regulatory frameworks through a shared control library. A single control can satisfy requirements from several frameworks simultaneously, so organizations do not need to gather separate evidence for each framework. According to customer data, this approach has delivered a 40% reduction in evidence requests through de-duplication, significantly reducing the compliance workload on IT and security teams.
MetricStream Cyber GRC includes IT and cyber policy management capabilities that enable organizations to create, communicate, and maintain IT and cyber policies across business units and global locations. Policies are mapped to asset classes, requirements, risks, controls, processes, and regulations. Automated policy review cycles, employee attestations, and exception management workflows ensure that policies stay current and that compliance with policy requirements can be demonstrated at any time.
MetricStream Cyber GRC accelerates audit readiness by maintaining a continuously updated, evidence-linked record of IT and cyber control assessments aligned to standards such as ISO 27001, NIST CSF, and SOC 2. Pre-packaged content provides a head start on compliance program implementation, and automated workflows ensure that controls are tested, findings are documented, and remediation actions are tracked on schedule. This continuous readiness approach reduces the sprint effort typically required before an audit.