AI-Powered GRC Solutions Enabling Agility & Resilience
AI Powered Solutions Enabling Agility & Resilience
Accelerate Growth, Drive Risk-Aware Decisions..
Reduce losses and risk events with forward-looking risk visibility. Enable a modern and integrated risk management approach with real-time aggregated risk intelligence and their impact on business objectives and investments.

Recognized as a GRC Leader by Industry Analysts
#12 in Chartis RiskTech 100 Report 2024
MetricStream Ranks #12 in Chartis RiskTech 100 Report 2024 and recognized as Category Leader in Enterprise Governance, Risk, and Compliance
Read more
Leader in Governance, Risk, and Compliance Platforms

MetricStream named a Leader in The Forrester Wave™: Governance, Risk, and Compliance Platforms, Q4 2023
Read moreLeader in Chartis Research GRC Solutions
MetricStream named a Leader in Chartis Research GRC Solutions, 2023 Market Update and Vendor Landscape
Read moreRecognized as a GRC Leader by Industry Analysts
Hear From Our Customers
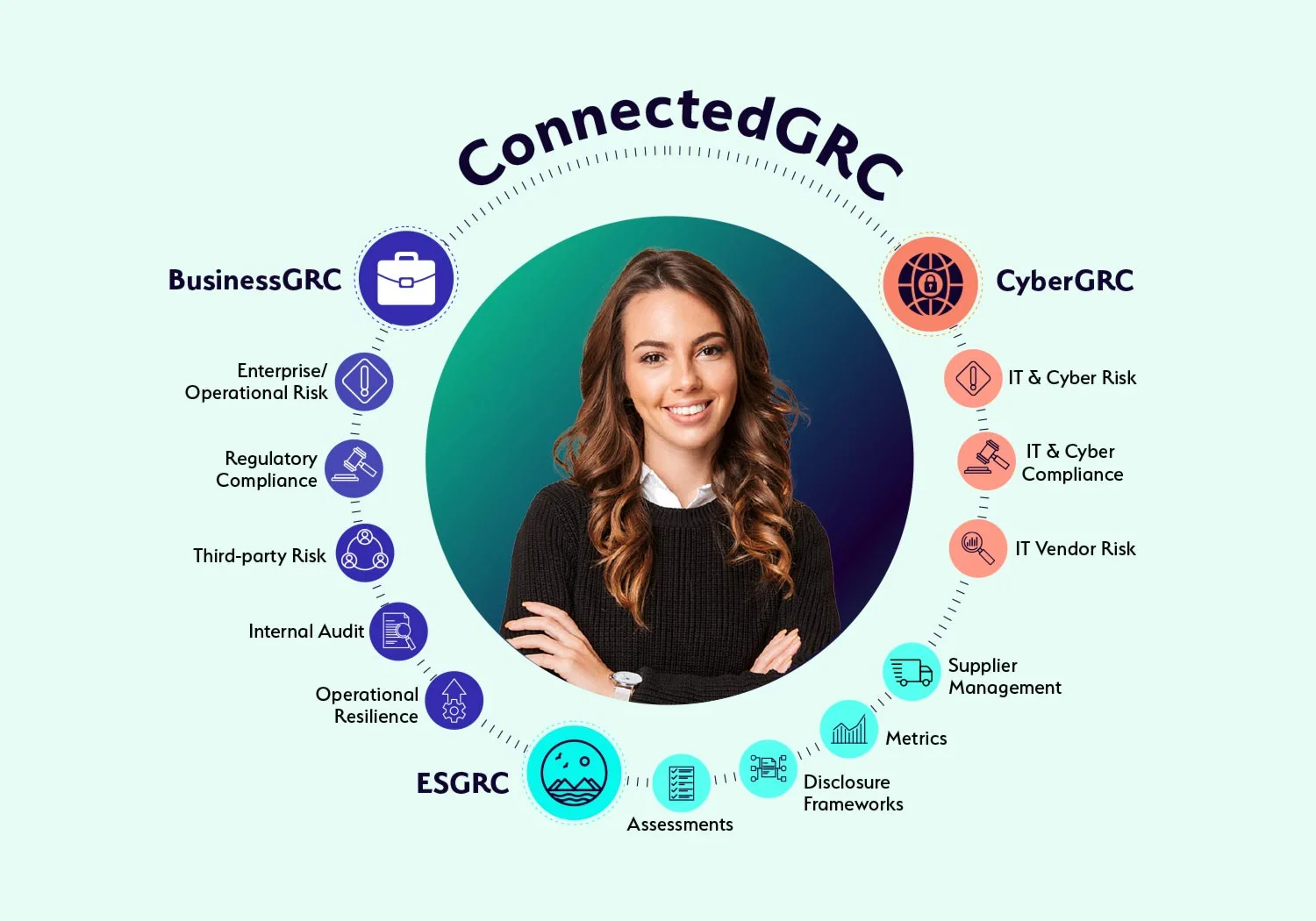
Why Choose a Connected GRC Platform?

Today’s dynamic enterprises require a connected to governance, risk, and compliance to better assess, manage, and mitigate risk across the enterprise. With MetricStream ConnectedGRC, your organization can:
Enhance decision-making with real-time insights into risk and compliance posture
Reduce risk exposure and losses, avoid risk of compliance violations, improve investments in growth, and gain a competitive advantage
Improve risk preparedness with better risk visibility and foresight through a proactive GRC approach