Cyber Resilience: The New Paradigm for Cyber Risk Management
- IT Risk & Cyber Risk
- 01 March 21

Introduction
With the growing frequency and sophistication of cyberattacks, cybersecurity leaders are on high alert to implement and maintain an effective and sound cybersecurity program. Cyber risks and the challenges of ensuring robust cyber health are further exacerbated as the digital interconnectivity of people, processes, and organizations continues to intensify.
Cyberattacks are growing at an alarming rate and do not show any signs of slowing down. Attacks on web applications alone surged by a whopping 800% in the first half of 2020, according to a report by CDNetworks. The Center for Strategic & International Studies (CSIS) estimates that cybercrime costs the world nearly $600 billion every year. Furthermore, private sector companies are expected to lose $5.2 trillion in revenue to cybersecurity attacks over the course of five years, from 2019 to 2023, as per a report from Accenture.
It is important to note here that organizations are often not the victims of a targeted attack, such as hacks, DDoS (Distributed Denial-of-Service) attacks, and others. Untargeted attacks, such as those carried out via malware (worms, spyware, adware, computer viruses, etc.), phishing emails, etc., are not directed towards any specific person or business and are more common. These attacks indiscriminately infect devices, casting a net as wide as possible. According to CSO Online, phishing attacks account for over 80% of reported security incidents.
Today, organizations simply cannot assume that they can have an impenetrable cyber defense mechanism. As such, the global narrative has been gradually shifting from cybersecurity to cyber resilience in recent years—focusing on not just averting cyber breaches but also designing a strategy to minimize impact and potential loss and ensuring continued business operations during the attacks.
Cyber Resilience—Daunting Yet Possible
As cybercrime incidents continue to proliferate across the globe, achieving cyber certainty seems to be a pipe dream for companies. Achieving cyber resilience, however, is not only a realistic goal but also indispensable for businesses to thrive in this digital era.
Embarking on the path to achieve cyber resilience starts with the identification of the cyber threats that an organization is exposed to (such as ransomware, malware, phishing attacks, etc.), prioritizing the risks depending on the impact and probability of them occurring, and devising an effective response plan. In today’s digitized world, checking an organization’s cyber health has become an iterative process requiring continuous monitoring of business processes and IT infrastructure for identifying and addressing any vulnerable areas or loopholes.
Achieving the state of sound cyber resilience could be a daunting proposition for any organization. It has been noted that quite often organizations put more reliance on tools and techniques for building cyber resilience capabilities rather than the expertise of people and well-designed processes. The best practice is to find the right mix of people, processes, and technology while devising the cyber resilience management framework.
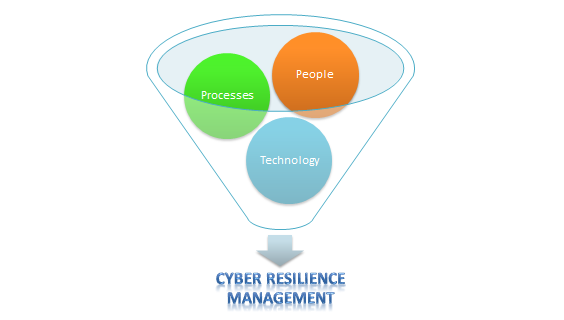
A cyber resilience framework is a structured approach that helps organizations proactively prepare for, effectively respond to, and swiftly recover from cyberattacks. It provides a comprehensive strategy to manage cyber risks.
An effective cyber resilience management program also requires integrating cybersecurity into business strategy and engaging the entire spectrum of stakeholders in the process for better decision-making.
MetricStream is helping organizations achieve cyber resilience in a simplified and streamlined manner, saving time, effort, and resources. With the MetricStream CyberSecurity Solution, organizations can proactively anticipate and mitigate IT and cyber risks, threats, vulnerabilities; have a 360-degree, real-time view of IT risk, compliance, policy management, and IT vendor posture; and implement an effective business continuity and disaster recovery program.
The Regulatory Perspective
International standard-setting bodies and national-level regulatory bodies are regularly publishing policies, guidelines, best practices, and more to help organizations prevent or mitigate cyberattacks.
The International Organization for Standardization (ISO), an international standard-setting body composed of representatives from various national standards organizations, has published ISO/IEC 27001 which provides requirements for an information security management system (ISMS). There is also the ISA/IEC 62443 series of standards, developed by the ISA99 committee, which provides a framework to address and mitigate existing and future security vulnerabilities in industrial automation and control systems (IACSs).
In addition to these global standards, there are various national standards such as the NIST Cybersecurity Framework, Cybersecurity Maturity Model Certification (CMMC) in the United States, Cyber Essentials in the United Kingdom, and the BSI IT Baseline Protection Catalogs in Germany, among others, which are intended to strengthen the cyber resilience of organizations operating in these countries.
Governments have also put into effect various cybersecurity regulations that govern the cybersecurity measures implemented by organizations. In the U.S. for example, healthcare organizations have to comply with the Health Insurance Portability and Accountability Act (HIPAA) while financial institutions have to adhere to the Gramm-Leach-Bliley Act. Organizations in the European Union have to adhere to the Network Information Security Directive, EBA ICT guidelines, the General Data Protection Regulation (GDPR), and other such regulations.
In 2020, the World Economic Forum created the Partnership against Cybercrime initiative that aims to explore ways to support and strengthen public-private cooperation against cybercrime and overcome existing barriers to cooperation. Such initiatives are particularly important for reinforcing the fight against cybercrime by businesses and regulators alike.
To conclude
The lack of a mature cyber resilience program and the resulting inability to thwart cyberattacks or minimize their impact can not only lead to regulatory fines and penalties but also reputational damage, loss of customer trust, and even threaten the very existence of a company. Public-private collaborative efforts to fight cybercrime, bringing together their respective strengths, capabilities, and resources, could go a long way to control the growing menace of cybercrime.
To learn more about cyber resilience read MetricStream’s eBook, A Shift from Cybersecurity to Cyber Resilience, which delves into the growing focus on cyber resilience management, the importance of cyber risk quantification, and provides quick tips on cyber resilience best practices and how to combat cyberattacks effectively with a cybersecurity incident response program.








