5 Simple Tips To Make Strong And Robust Business Continuity Plans
- IT Risk & Cyber Risk
- 23 November 16

Business Continuity Plans
Today’s organizations need comprehensive and robust business continuity planning for swift and effective action in case of a disaster or crisis. As the trade and supply chain have gone global, businesses today expect crisis response to be in seconds, not in hours, to ensure that the ripple impact is minimized. As organizations go digital, an IT failure can cripple the whole supply chain and business operations, causing extreme losses within hours and requiring countless hours to recover from the them. Plans to mitigate IT failures are also affected by the complexity of today’s IT infrastructure. As applications and systems are added based on business and market requirements, newer technologies and infrastructure pose new challenges.
Most businesses leverage cloud based platforms for their enterprise needs at least partially. The cloud helps businesses minimize costs and maximize efficiency; made for speed and convenience, it can scale up and down as needs demand and bring flexibility to business operations. However, the added overhead of managing cloud data centers, planning and performing test exercises across multiple locations and vendors as well as managing a crisis recovery, requires that organizations pay critical attention to their cloud solutions in combination with legacy infrastructure.
Today, an effective business continuity plan requires dynamic collection of information across the extended organization in a continuous manner. Organizations need to overcome the traditional fragmented approach to business continuity and formulate the business continuity strategy that adheres to the following five-point agenda:
1. Champion Business Continuity at the Highest Level
With senior management sponsorship, the business continuity plan will occupy its rightful position, high up in business priorities. This is important for sufficient budget, resourcing and training to be assigned to it. Senior leaders must set the tone at the top by insisting on robust crisis planning and regular reviews as a standard practice rather than a mere formality.
In August, Delta suffered a major IT outage that resulted in a $100 million loss in revenues for the airline. The impact was far-reaching, affecting check-in systems, flight information screens, the airline’s website and smartphone apps. The disruption to customers was extensive as well.
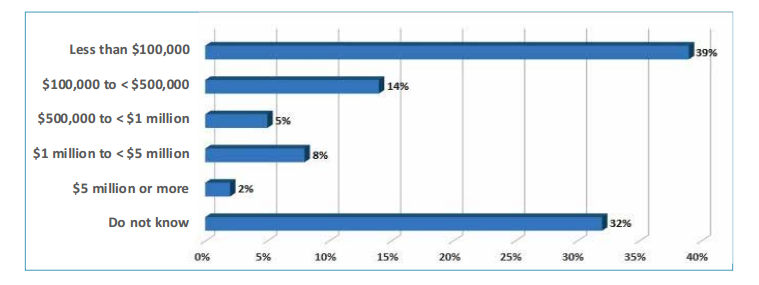
This is just one example of many; unfortunately, downtime of one type or another is a common situation in business. According to the Continuity Insights and KPMG, Global BCM 2016 report, 39 percent of global organizations have estimated the cost of business disruption to be $100,000 or less and 27 percent have estimated business disruptions ranging from $100,000 to $5 million or more in the last 12 months . This highlights the need for robust business continuity planning, championed at the highest level.
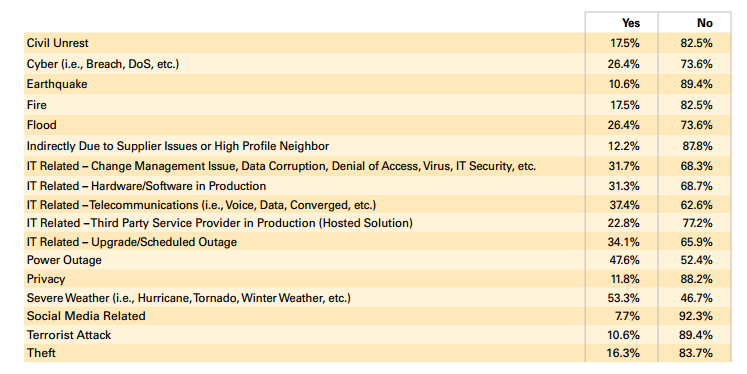
Types of Instances and Interruptions in Past Year
2. Review, Update and Test Regularly
The business continuity plan is a living document; it isn’t one to be created, filed and never looked at again. Risks evolve. Exercising the plans on a regularly scheduled basis will ensure businesses keep pace with the changing environment and understand what’s needed to protect critical infrastructure and preserve operations during a physical or virtual attack. Companies must learn from their own experience. Worryingly, according to Forrester and the Disaster Recovery Journal, 33 percent of businesses who had to invoke a business continuity plan, said one lesson learned from the experience was that the plan was out of date. Yet, 60 percent never carry out a full simulation of their business continuity plan for the entire organization; most walk through the plan as a document review.
It is of utmost importance that business continuity plans be reviewed by senior management and the planning team. Also, test results should be periodically evaluated and reported to the board, to assess the nature and scope of any changes to the organization’s business.
3. Include Partners, Suppliers and Third Parties
Companies don’t pay enough attention to the significant role of partners, suppliers and third parties in their business continuity. Deloitte found that over 94 percent of survey respondents had low to moderate confidence in the tools and technology used to manage third party risk and 88 percent felt the same about risk management processes. This, despite 87 percent having experienced disruption in the past three years that involved a third party.
Business continuity planning and disaster recovery has to be part of early third party discussions with responsibilities documented in service level agreements. Plans need to be aligned so that it is clear and easy to identify who does what, and where the handover points are when a plan is executed. The tools and systems used for collaboration must support transparency of information so that both parties are able to work from up to date information and take swift action in the event of a crisis.
4. Prioritize Ongoing Business Operations
The continuity plan should demonstrate that the business understands the priority level of its systems and that mitigating plans are in place to restore core operations as quickly as possible.
In the case of the Delta crisis, the outage was so extensive that it paralyzed business critical operations. The range of problems that can disrupt business – natural disasters, industrial action, cybercrime, IT failures, political or economic upheaval, suppliers ceasing to trade and so on – is so vast, and the systems and operations that can be impacted can be so wide that prioritization is a must.
A cloud-based option provides many benefits as an off-site back-up solution to ensure the efficacy of your continuity plan. However, as you develop your plan, ask yourself if a cloud-based option would increase the efficiency and cost-effectiveness of your plan and cover off essential considerations such as due diligence and service reliability with their provider. Another option is establishing a back-up plan that is independent of the cloud by leveraging personalized file backups, cross-device continuity solutions and communication software. The main aim is to get back faster and limit the amount of time that you’re spending without access to critical systems and information, by having a clearly defined continuity plan in place.
5. Define the Communications Plan Clearly
The business continuity plan has to be absolutely clear on how all stakeholders are going to be kept informed and how to enable upstream and downstream communication channels in times of crisis. Stakeholders include employees at all levels of the organization, such as suppliers, partners and customers.
The goal of the communications plan is to outline the channels and mechanisms for the sharing of information that will support efforts to resolve an issue at hand and limit the extent of its damage. How a company handles a crisis has an enormous impact on how they come out of the incident – people remember how the organization dealt and reacted to the issue and how convincing they were over the company’s efforts to make things right. For this reason, crisis management communications must be engaged at the earliest opportunity.
Service disruption is damaging to all businesses not only in terms of immediate revenue loss but also in the longer term brand and reputational impact. The business continuity plan is an essential, living document that aims to protect the ongoing sustainability of the business. Those that plan and execute well will see better performance in the long-run and be best-placed to weather the storms, whatever form they take.
The original article was published in Cloud Tweaks. You can view the article here.
Ensuring Resilient Cyber Safeguards in Cloud Applications
- IT Risk & Cyber Risk
- 12 October 16

Assessing Cloud Application Vendors from a Security Perspective
Enterprises of all structures and sizes across the globe have been adopting cloud for all needs – for computing, storage, databases, to hosting business applications. They are also proactively addressing cyber-security needs – both as dictated by internal Info-Sec controls, as well as those coming from external regulatory mandates.
For enterprises looking out for new cloud applications, I think one needs to look deeper and go beyond ‘checking the box’, which is typically done by looking at Compliance Standards around SOC2 controls, PCI-DSS, HIPAA, etc. This deeper insight can be gathered by looking at few key areas as follows:
- Underlying cloud infrastructure approach – Is it multi-tenant or multi-instance? I believe a multi-instance strategy that ensures there is no co-mingling of data across customers in the back end provides a sounds foundation for security because of the physical segregation that it leads to. There are other benefits in terms of performance and SLAs, as well.
- Encryption with key management should rest with the enterprise and not the cloud provider. This capability provides the necessary foundation for ensuring that you and the enterprise can decide where and how to provide encryption, and align it to your business needs. This will help you stay independent of your cloud provider.
- Look for how user entitlement is managed. Cloud applications need to have a sophisticated org-role construct for the segregation of duty. Often, cloud applications have only a role-based primitive to decide what a user can do in the application. However in real life, people change roles, sometimes people have to do multiple things, and as such applications that support more sophisticated models (such as a Federated Org-Role-User Mapping) are able to ensure they not only address such real life scenarios in a robust manner but in addition they are able to effectively maintain segregation of duty.
- Cloud Vendors that implement automated scans and audits around the full stack go a long way in providing security assurance. This should include hardware vulnerability management, OS patching, and application penetration testing, to application segregation-of-duty testing. In short, it should be an automated machinery that keeps a constant vigil and enforces periodic remediation.
- Finally, not all cloud application vendors will disclose their software development practices, but it is worthwhile to look at those and ask pointed questions to ensure OWASP standards, security testing (ideally by an external third party), and other Secure Software Development Life Cycle approaches are followed.
I am not prescribing that all the above 5 should be met, but the above vectors should be used to arrive at an assessment. Based on that assessment appropriate security controls can be implemented to get the full business benefit of a cloud application.
The New Reality of Risk
- Risk Management
- 28 September 16

Introduction
2016 has been a year of significant change; a year in which a sky full of hobbyist drones has become the norm; a year that has witnessed a new breed of terrorism that has shaken the world’s strongest governments; a year in which corporate governance scandals splash time and time again across the front-page news.
The Three Top Concerns for Leaders Around the World
There are three key trends that are capturing the attention of CEOs and government leaders, and fundamentally changing the way we live and do business – the introduction of left field disruptions, the risks and opportunities of global business ecosystems, and the rise of the digital universe.
Left field Disruption
In a recent survey of 25,000 plus CXOs conducted by a large public company, CEOs have come out with one common concern; “disruption from the left field.” Left field disruptions are the competitive threats that come from nowhere – they are the things that organizations did not predict or expect. Uber is a perfect example; in less than five years, Uber is now disrupting automotive, auto rental, transportation and even logistics industries. We also live in the era of left field cyberattacks, the rise of ISIS, the precipitous drop in oil prices. These left field disruptions are precisely what are keeping leaders up at night.
Risks and Opportunities of Global Business Ecosystems
Another topic that is top of mind for government leaders, boardrooms and CEOs is how to fully leverage the opportunities that exist in today’s global business ecosystems of partners, suppliers, and freelancers. McKinsey predicts that over $300 billion dollars’ worth of work will be freelanced in less than one decade. As our organizations go global and become more freelanced and outsourced, the question becomes this: how do we ensure that governance, risk management and compliance touches not just our employees, but extends across and embraces this entire ecosystem of partners and suppliers globally? In today’s global world, we are only as strong as our weakest link. Regulators are stepping up their focus on understanding an organization’s reliance on its networks of suppliers and partners, as well as the risks and vulnerabilities associated with global business ecosystems.
Rise of the Digital Universe
The other item that is top of mind for world leaders is how to harness the rise of the digital universe. We are living in exciting times, in an era where everything is being digitized and connected in the blink of an eye and at an unnerving pace. Nike recently announced their self-tying shoes with Internet of Things (IoT) sensors. Robots and drones are going to be the future for national defense and the new normal for logistics and manufacturing operations. Driverless cars are fast becoming a reality. IoT is connecting billions of devices. As new types of diverse data sources emerge, we have to know how to absorb that data and make sense of it.
The Power of Technology
Technology today seemingly has no limits. It is surprising to many just how much data is being generated at our very fingertips. For example, fitness wearables can collect data that could one day revolutionize the pharmaceutical industry. Analytics and big data can equip organizations and governments as they collect vast amounts of information, discover patterns and correlations, and understand behavior at scale. This may also be the key to mitigating today’s risks proactively, rather than the retroactive approach we have seen agencies and organizations put to practice in the past few years. Just imagine if federal agencies could design systems for this very purpose, with privacy in mind from the start, running behavior analytics to identify 1 billion people with the confidence that it does not pose a threat to our security. From there, agencies could focus their efforts on the other 6 billion people, and continue to sort through to find the bad actors. This system may seem radical, but when you consider that proactive checks like these already exist (i.e., TSA’s Precheck program), it becomes an increasingly logical option for the world as we know it today. At the moment, this is not happening. We are reactively firefighting in the dark; going after the bad actors when it is already too late. What we need to do, instead, is to proactively solve the problem by bringing in light, transparent, and sophisticated analytics. What we need to do is to push ourselves to anticipate challenges and implement effective solutions for risks that lie ahead; we need to make this our mission for the months and years ahead.
Looking Ahead
We are certainly on the brink of a new reality, living in a world of left field disruptions, global business ecosystems, and the rise of the digital universe. Leadership, no doubt, has an obligation to give this new reality special attention; to find new and improved ways of adapting, planning, and executing. Yes, there is a need, and expectation, to understand both the sides of the equation – the risks and the opportunities. We also need to avoid getting caught up in fear and panic due to the news and the headlines we read each morning.
While there are new risks cropping up all around us, for a business, it is essential that opportunities are identified from these risks. So, what kind of leadership can help lead us towards advancement within this new reality? Leaders, whether they are at the wheel of a technology company, a government agency, or a product reseller, must rethink their operating methods, and identify proactive steps that bring about transparency and opportunity in a world of risks. Leaders must take on the task of identifying and understanding risks, and at the same time not be burdened by fear – fear that cripples evolution and innovation. While the world continues to change right before our very eyes, our collective mission must be on strategies and solutions that help open new doors, and continue to break down barriers and boundaries.
How to Mitigate Risk Exposure from Vendor Relationships
- Risk Management
- 26 September 16

Introduction
Outsourcing business activities to a vendor does not include outsourcing the risk and compliance responsibilities. Relying heavily on vendors, with low or limited visibility into the vendor networks, exposes organizations to high risks. Therefore, understanding and managing vendor risks is crucial to maintain sustainable businesses. With a strong Vendor Risk Management (VRM) program companies can anticipate inherent risks rather than simply reacting to adverse situations and incidents after they occur.
In many organizations, VRM programs are largely traditional. The focus is on managing vendor risk only when selecting a vendor or finalizing a vendor contract. However, for VRM to be truly effective, there is a need for continuous vendor monitoring which helps organizations be well-prepared for unexpected eventualities. That being said, it can be quite a challenging task to define and adopt an efficient VRM program, as multiple factors need to be considered, including dependency on the vendor, the location and financial stability of the vendor, as well as the scope of the vendor relationship. This is where technology can help by significantly automating and simplifying vendor risk assessments.
Companies are increasingly focusing on strengthening VRM through best practices such as:
- Effective vendor selection process
- Streamlined due diligence and continued oversight
- Structured vendor risk assessment approach
- Efficient vendor performance monitoring
- Disciplined vendor governance framework
Technology embedded with these best practices can help companies manage vendor networks, associated risks, and compliance requirements. Here are some of the reasons why a robust VRM technology platform should be a top priority for any business:
- Optimizes VRM processes
- Consolidates vendor information
- Centralizes contract management
- Facilitates early detection and mitigation of risk
- Makes Business Resilient
- Enables Vendor Evaluation and Training
- Provides robust analytics and reporting
An organization’s approach to VRM can significantly affect its ability to achieve its goals. There is a greater need to understand the risks posed by vendors as well as fourth parties, while also keeping pace with regulatory changes. Technology plays an important role in this effort by helping companies map vendor risks to the associated regulations, controls, internal stakeholders, and vendors, thereby improving risk transparency and accountability. It helps ensure that companies have all the information they need to meet the demands of a changing regulatory environment. And finally, it streamlines the flow of vendor risk and compliance data, so that the right information reaches the right stakeholders at the right time.
To view the details of best practices adopted by organizations for effective Vendor Risk Management and the role of technology, you can read more here
Governance, Risk, Compliance and the Big Data Advantage
- Audit Management
- 24 September 16

Introduction
According to a leading IT firm research nearly 90 percent of the data in the world has been produced in just the last two years. Though a bit of a buzz phrase these days, big data is as important as the internet itself to many businesses today, for a number of reasons. The simplest explanation of how big data benefits businesses is this: It provides the insights needed to make more confident decisions, take faster actions, improve operational efficiencies, minimize risks, and reduce spending.
The sudden emergence of the whole phenomenon around the data explosion has been the result of the pervasive use of mobile devices and the large volumes of data generated from web based purchases, mobile activities, and social media interactions. As the massive volume of data and computing platforms continues to proliferate, the absence of thorough reassessments and thinking around information processing paradigms of the past will leave today’s enterprises ill-prepared to deal with this new (IT) normal.
Enterprises have to realize the obvious fact that big data is an immensely powerful concept, and information is a strong business asset. Managing large volumes of homogenous data is something that organizations of all kinds can benefit from; spanning retail, social networking, science and research, clinical trials, CRM, operational activities, transactions and more. The real challenge for organizations today is to move beyond the data volumes and data storage obstacles to assess the true value of available data to reduce overall internal audit or compliance field work costs. The vast majority of enterprise businesses are faced with the challenge of decoding large volumes of homogenous, inconsistent, or inaccurate data — often referred to as “bad data.”
Industry analyst Doug Laney encapsulated the characteristics of big data using the three Vs — volume (the quantity of data), velocity (the rate at which data is generated and changed) and variety (the number of different data sources and types). Many are also adding characteristics such as “complexity,” “veracity” and “variability” to their understanding of the concept.
An accurate analysis of big data helps enterprises with better insights into their customers, market opportunities, growth prospects, and corporate performance. This strategic analysis of large volumes of data enables organizations to achieve higher-quality results in their own internal audit and compliance processes, thus enabling them to establish more effective governance, controls, and monitoring mechanisms.
With the skyrocketing number of transactions and evolving compliance requirements and regulations, big data analysis offers endless opportunities for enterprises to mitigate key governance, risk, and compliance issues. Just as big data analytics can lead to more targeted marketing initiatives by analyzing marketing program responses, supplier activities, customer demographics, and sales patterns, effective analysis of massive volumes of structured and unstructured data can also enable organizations in the Governance, Risk and Compliance (GRC) space to:
- Develop strong risk intelligence to strengthen risk management and streamline regulatory compliance
- Identify high-risk vendors/persons with multiple fraud risk indicators in accounts payable
- Display travel and entertainment expenses of local office employees
- Identify the best practices in the industry to effectively mitigate risks
- Determine if control procedures are working effectively
Big data analysis should become a core component of every organization’s operations, performed on a continuous basis, spanning areas such as payment or billing transactions, payroll, social media analysis, sales, operational processes, and compliance. For many organizations, especially in highly scrutinized and regulated industries such as healthcare, finance, and insurance, big data analysis can support Enterprise Risk Management (ERM) by helping monitor risks involving loans, claims, and patient care procedures.
Simply stated, integrating big data analytics into an organization’s GRC methodology will help pave the way for a truly data-driven organization.
So, Where’s My IT-Risk (Or Threat) Library?
- IT Risk & Cyber Risk
- 04 August 16

Introduction
We need a good information security risk and threat library. Rather than build one from scratch (and most internet searches do not yield meaningful results), we were wondering if MetricStream offers standard content for such a library.
That’s a question we’re frequently asked when we get a Customer up and running with MetricStream’s IT-Risk Management App. It’s an excellent question for sure because Customers, especially in the Governance, Risk, and Compliance space, require preloaded (and expert/industry-grade) content that can get them up and running on day one. The content ask is straightforward when it comes to in-depth content from authority documents (individual citations or sections and sub-sections), control statements, or even policy templates. Citations from an authority document wouldn’t change across Customers and control statements too are uniform especially if you leverage upon a harmonized control framework.
Information security risk content (threats, vulnerabilities, and risks) is, however, in a league of its own – perhaps in the league of extraordinary content. Prima facie, it’s pretty easy to be misled into believing that information security risks applicable for my business are exactly the same as those applicable for your business because, hey, come on, we’re both using information technology right?
In reality though that’s precisely where the differences arise. Information technology in the context of my business’ operating and technology environment are almost always completely different in the context of your business’ operating and technology environment. Here’s an example: Suppose we have two Customers, a Technology Infrastructure Provider and a Healthcare Provider. The Technology Infrastructure Provider is primarily concerned with risks around specific technologies being used (unpatched systems, insecure configurations, root or elevated access, availability and continuity, etc.), environmental factors (fire, flood, etc.) and such whereas the Healthcare Provider is primarily concerned with risks around identity and access management (patient data falling into the wrong hands), data integrity (patient data cannot be tampered with as it moves from system to system), and such.
A standard list of information security risks and threats is therefore not advised since that also allows for context bias to creep in – when we see a list our mental models are bounded by what we see on that list. As a best practice, MetricStream advises the following approach to building an information security risk and threat library:
- Identify the business stakeholders (publishers and consumers of a business process, business service, or business application). This step gives you a great idea of what exactly you’re trying to protect and why.
- Brainstorm possible causes (threat agents) and methods (threat factors) that can lead to business process/service/application disruption (vulnerabilities).
- Compare the outcomes from step 2 against popular threat catalogs. MetricStream advises picking from this list:CSA’s ‘The Treacherous Twelve’ Cloud Computing Top Threats in 2016
- NIST SP 800-30 Rev. 1 Appendix D
- If you have access to the ISO 27005 standards document one of the appendices within this document has a threat catalog.
Once you’ve identified the information security risks and threats that are actually applicable to your business’ operating and technology environment you can leverage upon MetricStream’s content import mechanisms to easily bring this library into the MetricStream IT-Risk Management App for the purpose of risk assessment, risk analysis, and risk treatment.









