Measure Your Program Outcomes
Source: Based on MetricStream customer responses and GRC Journey Business Value Calculator

0
reduction in the time taken to complete risk assessments

0
cost savings in risk assessment and related processes

0
time savings in tracking and linking policies to regulations
Protect Your Digital Enterprise by Reinforcing Cyber Governance
The MetricStream Cybersecurity Risk Management software solution is a part of the CyberGRC solution which enables organizations to stay ahead by proactively anticipating and mitigating IT and cyber risks, threats, vulnerabilities, and multiple IT compliance requirements. The solution helps streamline cybersecurity efforts to achieve cyber resilience. Built on the MetricStream Platform, the solution cuts across enterprise siloes, aggregating information and providing a 360-degree, real-time view of IT risk, compliance, policy management, and IT vendor posture. The solution also enables enterprises to execute and manage an effective business continuity and disaster recovery program.
READ MORE Product Description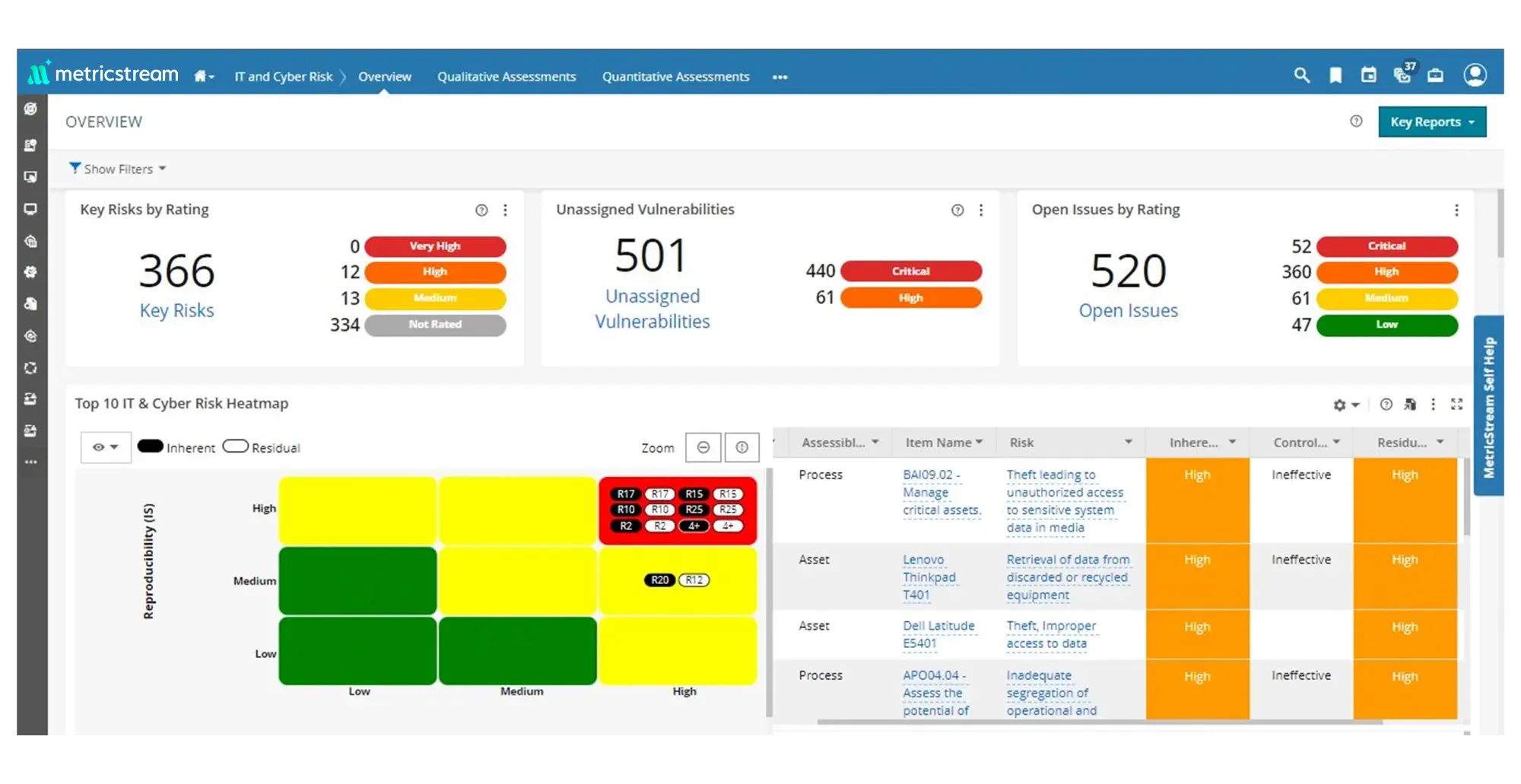
How Our Cybersecurity Risk Management Software Solution Helps You
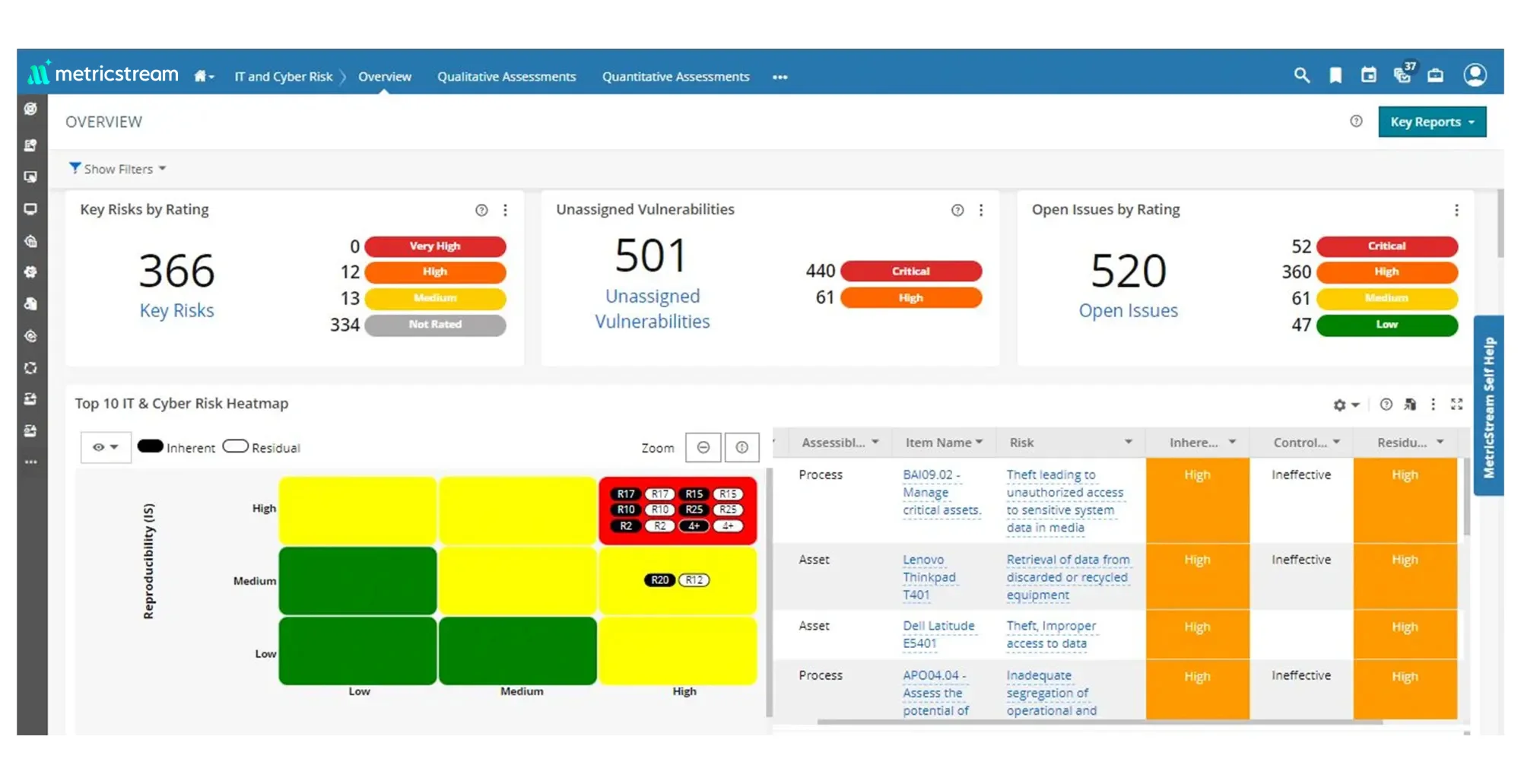
Comprehensive Visibility into Cybersecurity Risks
Define and maintain data on cybersecurity risks, assets, processes, and controls in a centralized repository. Assess, quantify, monitor, and manage cybersecurity risks using industry standards and risk assessment frameworks. Enhance visibility and gain contextual risk insights by mapping IT assets to cybersecurity risks, IT vendor risks, threats, and vulnerabilities and associated details such as description, category, hierarchy, ownership, and validity.
Consolidated Threat and Vulnerability Intelligence
Import, aggregate, prioritize, track, and remediate cybersecurity threats and vulnerabilities in an efficient, collaborative manner. Drive better-informed decisions on vulnerability remediation strategies by determining combined risk ratings for business assets based on the vulnerability severity and the asset criticality rating.
Robust Cybersecurity Compliance with Effective IT Controls
Manage and monitor compliance with a range of IT regulations and standards in an integrated manner. Maintain a centralized repository for all associated processes, assets, risks, controls, and audits. Harmonize control sets across multiple regulatory requirements to eliminate duplication of controls. Assess and manage IT controls in an integrated manner using industry standard frameworks such as ISO 27001 and NIST.
Continuous Control Testing and Monitoring
Set up autonomous processes for the continuous testing and monitoring of your cloud security controls. Adopt a proactive approach to identifying vulnerabilities and control weaknesses to strengthen cloud security. Strengthen compliance posture by mapping cloud security controls with your internal controls that are aligned to compliance standards, such as HIPAA, NIST CSF, PCI, and ISO 27001.
Cyber Risk Quantification
Quantify cybersecurity risk in business and monetary terms, enabling proactive communication and management of risk exposure. Drive better-informed cybersecurity investment decisions with support from the FAIRTM model. Improve accuracy in determining the monetary impact of cybersecurity risks such as data breaches, identity theft, infrastructure down time, etc.
Efficient Business Continuity Planning
Easily maintain and carry out business continuity plans from templates and map them to associated business processes and functions, critical resources, IT assets, key contacts, and locations. Regularly assess the business continuity plans to check if the outlined activities are relevant and effective.
AI-Powered Intelligent Issue Management
Identify and document issues from cybersecurity risk and compliance assessments through a closed-loop process of issue investigation, root cause analysis, and remediation. Leverage AI-powered capabilities to identify issues based on relation and recommend issue classification in a quick and efficient manner.
How Our Cybersecurity Risk Management Software Solution Benefits Your Business
- Build confidence with executive management, regulators, and other stakeholders by adopting an enterprise-level approach to cybersecurity risk management and resilience
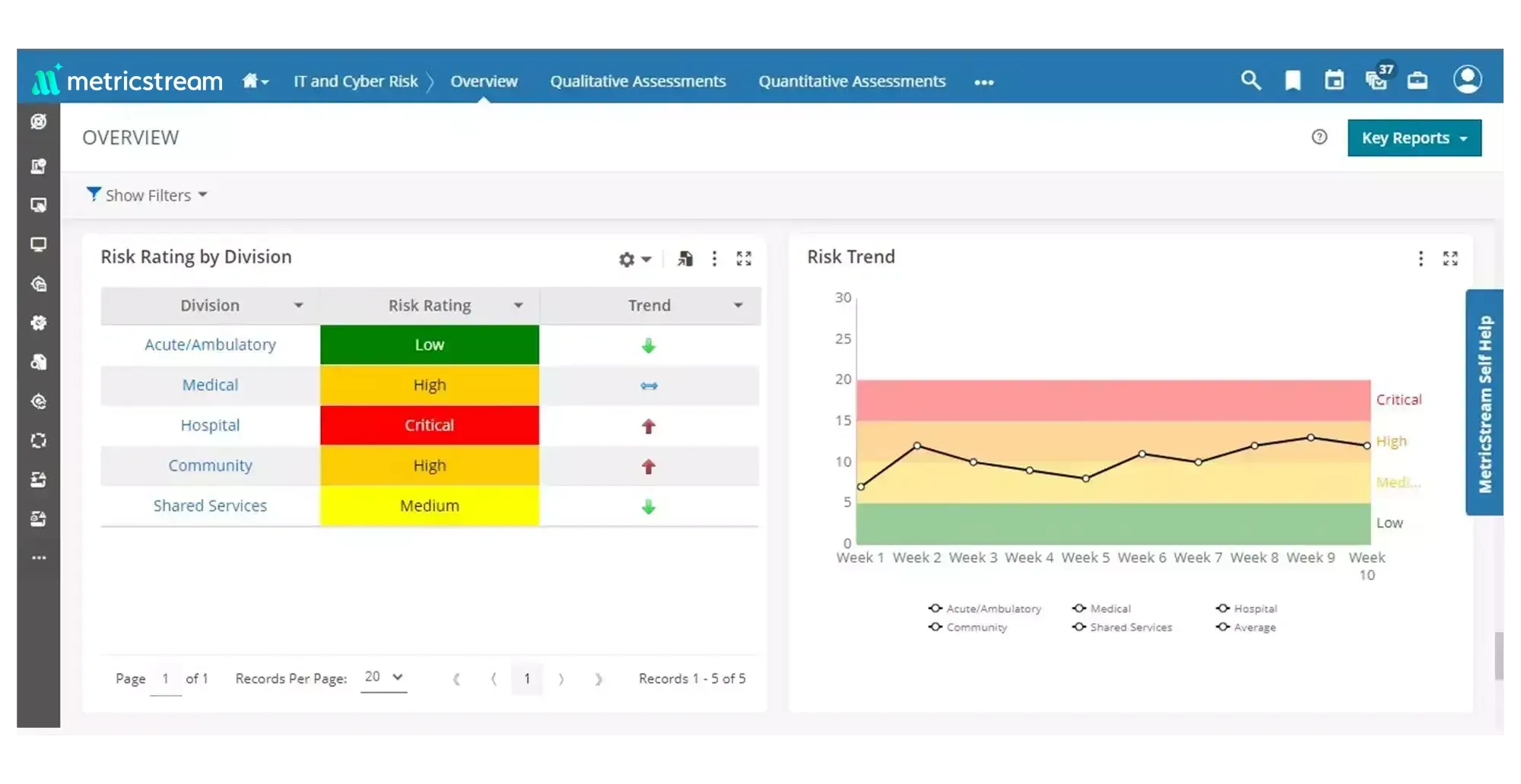
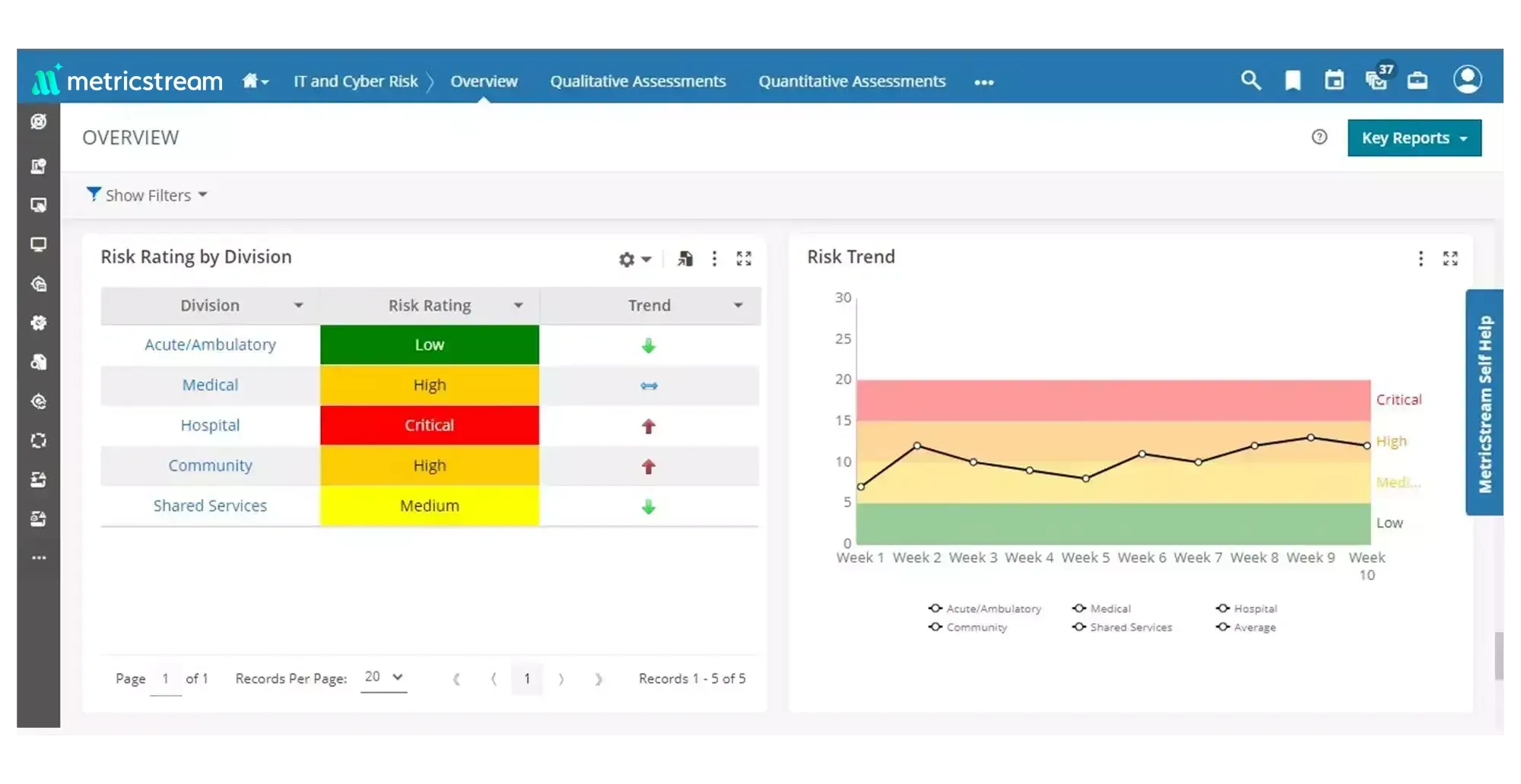
- Gain real-time visibility into cybersecurity risks and threat exposure through quantified and contextual risk information from across processes and assets
- Optimize efficiency by correlating cyber vulnerabilities with IT assets and prioritizing remediation measures based on criticality
- Drive better-informed cybersecurity investment decisions and improve communication of cyber risk exposure to the top management and the board
Frequently Asked Questions
MetricStream's Cybersecurity Solution provides a single platform for managing cybersecurity-related risk and compliance activities including IT and cyber risk management, compliance management, policy management, and IT vendor risk management. It aggregates and integrates data on IT and cyber risks, threats, compliance obligations, policies, and controls across enterprise silos, and delivers a 360-degree, real-time view of the organization's cyber risk and compliance posture through powerful dashboards and reports.
According to customer responses and the GRC Journey Business Value Calculator, MetricStream's Cybersecurity Solution has delivered a 66% reduction in time taken to complete risk assessments, a 38% reduction in the cost of managing vulnerabilities and their impact, and a 30% reduction in the number of work days required to manage a scaled-up level of vulnerability management.
MetricStream's Cybersecurity Solution helps CISOs anticipate and mitigate cyber risks by providing a continuous, integrated view of IT risks, threats, vulnerabilities, and controls across the enterprise. AI-powered issue identification surfaces related risks before they escalate, Cyber Risk Quantification capabilities express exposure in dollar terms to support investment decisions, and role-based executive dashboards communicate the cyber risk posture clearly to the board and regulators. This enterprise-wide visibility allows security leaders to act proactively rather than reactively.
MetricStream's Cybersecurity Solution manages compliance with IT regulations and governance standards—including SOX, FFIEC mandates, PCI-DSS, HIPAA, NERC-CIP, NIST, and ISO 27001/2—through a central compliance hierarchy that links regulations, processes, assets, risks, controls, and audits. Integration with the Unified Compliance Framework (UCF) maps over 9,300 IT control statements to more than 1,200 regulations. Automated alerts notify teams when regulatory standards change so they can respond quickly.
MetricStream's Cybersecurity Solution proactively aggregates and correlates threats and vulnerabilities across business-critical information assets. IT assets are consolidated from Configuration Management Databases (CMDBs) and mapped to associated threats and vulnerabilities. Integrations with endpoint IT security and infrastructure management tools and security intelligence feeds allow organizations to identify and prioritize risks across their full asset portfolio. Real-time graphical dashboards with drill-down capabilities report on threats and vulnerabilities by asset, severity, and business unit.
MetricStream's Cybersecurity Solution includes a dedicated IT Vendor Risk Management capability that provides a single point of reference for identifying, assessing, mitigating, and monitoring IT vendor risks. Vendor registration and onboarding are accelerated through automated workflows. Pre-defined questionnaires simplify vendor due diligence, and powerful analytics help management teams make informed decisions based on vendor risk, compliance, and performance data. This is especially important given that vendor IT systems often represent significant points of cyber risk exposure.
MetricStream's Cybersecurity Solution communicates cyber risk to the board using Cyber Risk Quantification capabilities that express risk exposure in dollar values, using the FAIR model. This financial framing translates technical cyber risk data into business-relevant metrics that boards and C-suite executives can readily understand and act on. Role-based dashboards with drill-down capabilities and customizable reports allow security teams to tailor board communications to specific audiences and regulatory requirements.
MetricStream's Cybersecurity Solution includes a Policy and Document Management capability that enables systematic management of IT policies across business units, divisions, and global locations. A centralized policy portal stores, manages, and provides access to IT policies. Policies are linked to regulations, risks, controls, and legal requirements, and automated notifications alert the target audience when policies are published or revised. Attestation workflows confirm that employees have read and understood each policy.
MetricStream's Cybersecurity Solution includes Business Continuity Management capabilities with pre-embedded plan templates, configurable scoring logic for calculating Recovery Time Objectives (RTO) and Recovery Point Objectives (RPO), and integration with Emergency Mass Notification Systems (EMNS). Multiple recovery strategies can be tracked through Gantt charts, and configurable dashboards highlight gaps between recovery requirements and current readiness. These capabilities ensure that cyber incidents are managed within a broader resilience framework.
MetricStream's Cybersecurity Solution reduces vulnerability management costs by consolidating vulnerability data from multiple scanning tools, prioritizing remediation based on combined risk ratings that weigh both vulnerability severity and business asset criticality, and automating the creation and tracking of remediation action plans. This structured, risk-based prioritization approach ensures that resources are directed to the most impactful vulnerabilities, reducing the overall volume of remediation work and its associated costs.